
SOC as a Service – Managed Security Services
Key Features of Swasti Datamatrix’s SOC as a Service

Benefits of SOC as a service
Maximizing Security Effectiveness: A Comprehensive CISO’s Guide to SOC as a Service, its Essentials, and Significance
PUNE, MAHARASHTRA, INDIA, September 25, 2023 /EINPresswire.com/ — 𝐒𝐎𝐂 𝐚𝐬 𝐚 𝐒𝐞𝐫𝐯𝐢𝐜𝐞𝐬 – 𝟐𝟒*𝟕 𝐈𝐧𝐜𝐢𝐝𝐞𝐧𝐭 𝐑𝐞𝐬𝐩𝐨𝐧𝐬𝐞
Today, security teams find themselves under immense pressure due to ongoing efforts by organizations to embrace digital transformation. This transformation expands the cyber-attack surface that these teams are responsible for safeguarding. The environments they work in have become incredibly complex and interconnected, resulting in a constant stream of alerts, the need for tedious tuning, and repetitive manual tasks. To make matters even more challenging, cybercriminals are evolving their tactics, introducing new, more complex attacks such as Ransomware-as-a-Service operations, all designed to avoid detection. As a result, businesses across various industries are feeling the impact of these challenges, with a staggering 84% of enterprises experiencing one or more breaches in the past year.
In today’s digital age, cybersecurity is paramount for businesses of all sizes. With the ever-evolving landscape of cyber threats, safeguarding organizations’ sensitive data and ensuring the continuous operation of online services/products is a top priority. Recognizing this need, Swasti Datamatrix has revolutionized the way organizations protect themselves from cyberattacks by offering a comprehensive Security Operations Center (SOC) as a Service.
SOCaaS provides continuous monitoring, threat detection, and incident response, backed by a team of dedicated experts and cutting-edge technologies. This proactive approach empowers businesses to stay ahead of cyber adversaries, ensuring business continuity, compliance, and reputation preservation in an increasingly interconnected and vulnerable digital world.
𝐀𝐥𝐚𝐫𝐦𝐢𝐧𝐠 𝐂𝐲𝐛𝐞𝐫𝐚𝐭𝐭𝐚𝐜𝐤 𝐒𝐭𝐚𝐭𝐬 𝐑𝐞𝐯𝐞𝐚𝐥 𝐆𝐫𝐨𝐰𝐢𝐧𝐠 𝐓𝐡𝐫𝐞𝐚𝐭 𝐭𝐨 𝐊𝐞𝐲 𝐒𝐞𝐜𝐭𝐨𝐫𝐬:
After carefully examining cyberattacks that were identified and prevented over a 90-day period, the BlackBerry Threat Research and Intelligence Team has documented the following statistics in their report:
● 1,578,733 malware attacks analyzed
● 200,454 unique attacks with undetected malware
● An average of 17,280 attacks per day
● 60% targeted finance, healthcare, retail
● Healthcare: 93,000 targeted attacks
𝐖𝐡𝐲 𝐘𝐨𝐮 𝐍𝐞𝐞𝐝 𝐒𝐎𝐂 𝐀𝐬 𝐚 𝐒𝐞𝐫𝐯𝐢𝐜𝐞?
The internet has become the most important channel for many businesses. Ten years ago, security teams had to deal with large volumes of people, assets, and locations. Today, the volume of data and traffic that businesses handle online is far greater. To protect against attacks, businesses need a reliable way to sift through all this traffic.
𝐂𝐨𝐦𝐩𝐫𝐞𝐡𝐞𝐧𝐬𝐢𝐯𝐞 𝐌𝐚𝐧𝐚𝐠𝐞𝐝 𝐒𝐎𝐂 𝐚𝐬 𝐚 𝐒𝐞𝐫𝐯𝐢𝐜𝐞𝐬:
– Advanced SIEM with User & Anomaly Behavior Analytics
– Timely and effective response to security incidents
– Threat Hunting & Vulnerability Management
– Expert advice on how to improve security posture
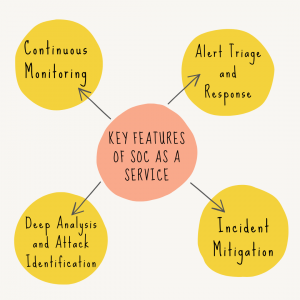
𝐊𝐞𝐲 𝐅𝐞𝐚𝐭𝐮𝐫𝐞𝐬 𝐨𝐟 𝐒𝐎𝐂 𝐀𝐬 𝐚 𝐒𝐞𝐫𝐯𝐢𝐜𝐞:
● 𝐂𝐨𝐧𝐭𝐢𝐧𝐮𝐨𝐮𝐬 𝐦𝐨𝐧𝐢𝐭𝐨𝐫𝐢𝐧𝐠: Security threats and operational disruptions can occur at any time. It ensures round-the-clock monitoring of the enterprise environment, offering real-time protection against emerging threats.
● 𝐂𝐮𝐬𝐭𝐨𝐦 𝐚𝐥𝐞𝐫𝐭 𝐭𝐫𝐢𝐚𝐠𝐞 𝐚𝐧𝐝 𝐫𝐞𝐬𝐩𝐨𝐧𝐬𝐞: SOCaas, augmented by cybersecurity experts, is equipped to handle custom alerts tailored to the organization’s specific needs. This ensures a swift and effective response to potential security incidents.
● 𝐃𝐞𝐞𝐩 𝐚𝐧𝐚𝐥𝐲𝐬𝐢𝐬 𝐚𝐧𝐝 𝐚𝐭𝐭𝐚𝐜𝐤 𝐢𝐝𝐞𝐧𝐭𝐢𝐟𝐢𝐜𝐚𝐭𝐢𝐨𝐧: With a vast pool of cybersecurity expertise, the SOC team conducts in-depth analysis to identify attack vectors and network outages. This proactive approach helps anticipate and mitigate threats before they cause significant damage.
● 𝐈𝐧𝐜𝐢𝐝𝐞𝐧𝐭 𝐦𝐢𝐭𝐢𝐠𝐚𝐭𝐢𝐨𝐧: In the event of an attack, the SOC team takes immediate action to implement countermeasures, reducing the impact of incidents and ensuring the continuity of online services.
𝐓𝐡𝐞 𝐁𝐞𝐧𝐞𝐟𝐢𝐭𝐬 𝐨𝐟 𝐒𝐎𝐂 𝐚𝐬 𝐚 𝐒𝐞𝐫𝐯𝐢𝐜𝐞:
SOC as a Service provides organizations with continuous monitoring, threat detection, and incident response capabilities. SOCaaS can help organizations improve their security posture, reduce their risk of cyberattacks, and meet compliance requirements.
● 𝐈𝐦𝐩𝐫𝐨𝐯𝐞 𝐭𝐡𝐫𝐞𝐚𝐭 𝐢𝐧𝐭𝐞𝐥𝐥𝐢𝐠𝐞𝐧𝐜𝐞: SOCaaS uses a variety of security tools and technologies to collect and analyze data from networks, endpoints, and applications. This provides a comprehensive view of security posture and helps businesses to identify and respond to threats more quickly.
● 𝐈𝐧𝐜𝐫𝐞𝐚𝐬𝐞𝐝 𝐯𝐢𝐬𝐢𝐛𝐢𝐥𝐢𝐭𝐲: SOCaaS provides 24/7 monitoring of the IT environment, so businesses can be confident that systems are being protected around the clock. It also has access to a dashboard that provides real-time visibility into security posture.
● 𝐀𝐮𝐭𝐨𝐦𝐚𝐭𝐢𝐨𝐧 & 𝐞𝐟𝐟𝐢𝐜𝐢𝐞𝐧𝐜𝐲: SOCaaS uses automation to streamline many of the tasks involved in security operations, such as threat detection and incident response. This frees up teams to focus on more strategic initiatives.
● 𝐏𝐫𝐨𝐚𝐜𝐭𝐢𝐯𝐞 𝐦𝐢𝐭𝐢𝐠𝐚𝐭𝐢𝐨𝐧 𝐬𝐭𝐫𝐚𝐭𝐞𝐠𝐢𝐞𝐬: Swasti Datamatrix’s SOCaaS team uses a variety of methods to identify and mitigate threats before they cause damage. This includes threat intelligence sharing, vulnerability scanning, and incident response planning.
Swasti Datamatrix is here to help businesses with their cybersecurity. Our SOC as a Service provides a single pane of glass for attack monitoring and mitigation.
As we navigate this dynamic cybersecurity landscape, we invite CISO’s or Security enthusiastics to explore our blog for further insights and guidance. Swasti Datamatrix is committed to being a trusted partner in the fight against cyber threats, and we’re here to empower organizations to thrive securely in the digital age. Stay secure, stay informed, and let us help businesses to overcome the top security challenges with SOC as a Service.
𝐑𝐞𝐥𝐚𝐭𝐞𝐝 𝐀𝐫𝐭𝐢𝐜𝐥𝐞s:
https://www.swastidatamatrix.com/blog/siem-vs-edr-vs-xdr-understanding-the-key-differences-and-choosing-the-right-cybersecurity-solution
https://www.swastidatamatrix.com/blog/how-a-security-operations-center-soc-can-help-you-overcome-your-top-security-challenges
https://www.swastidatamatrix.com/blog/the-power-of-siem-how-to-secure-your-it-environment
Suraj T.
Swasti Datamatrix
[email protected]
Visit us on social media:
Twitter
LinkedIn
YouTube
SOC as a Service Swasti Datamatrix Comprehensive Managed Security Services for Your Business
![]()






































